The Cybersecurity Maturity Model Certification is a hot topic in the cybersecurity world. The reason is that it has impacted a lot of companies around the globe that perform federal contracts. Since it’s relatively new, this has surprised some and left people with questions. Here are some frequently asked questions and answers about the CMMC.
What is CMMC?
The CMMC is now a required certificate for federal and DoD contractors to ensure that companies have all the necessary cybersecurity to protect sensitive data. The new version 2.0 combines a variety of best cybersecurity practices and standards to ensure that data is protected and cannot be attacked. Before CMMC was implemented, contractors were responsible for creating their cybersecurity measures. While contractors are still accountable for their cybersecurity, they now have specific standards that must be met, and typically a third-party assessment must be completed.
Who Needs This Certification?
The hundreds of thousands of large contractors, small businesses, and manufacturers working for the federal government and DoD require this certification. That includes those who work directly with the DoD and subcontractors that handle different tasks for federal contractors.
What is the Framework?
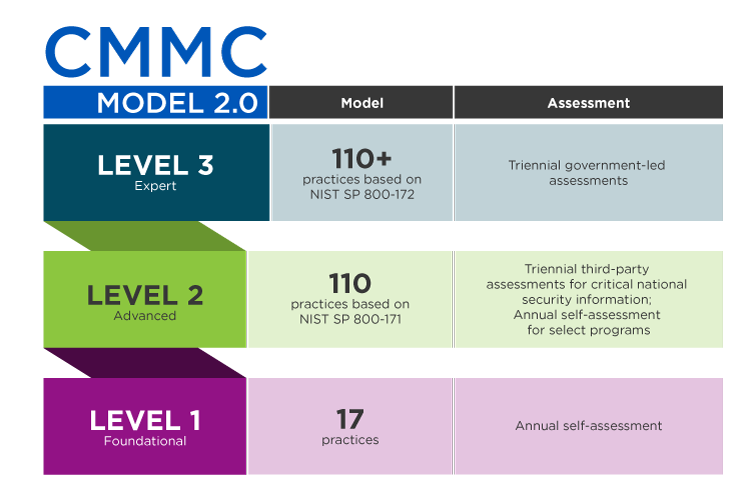
The overall framework for the CMMC is a three-tier system that categorizes companies based on their ability to protect data from cyber-attacks. Each of these levels has specific processes and practices that must be implemented to determine potential risks and the type and sensitivity of data that can be handled. These are organized into domains that address different aspects of cybersecurity.
What are the Domains?
Seventeen different domains affect a company’s cybersecurity level. Each of these domains must be met by a company to be certified as compliant. Its practices within each category determine what maturity level a company receives.
What are the Practices?
To receive a level one maturity rating, a company must implement at least one practice in each domain, meaning it must have at least 17 strategies in place. If a company wants to receive a level two rating, it must have 110 practices aligned with the security standard NIST SP 800-171. Finally, to receive a level three maturity rating, a company must have more than 110 practices aligned with security standard NST SP 80-172.
What are the Maturity Levels?
The government’s strategic approach to cybersecurity has resulted in different maturity levels that categorize a company’s security, which determines what activities and data it can handle. In version 2.0, there are three maturity levels, foundational, advanced, and expert, also known as one, two, and three.
Are PKIs Important?
CMMC compliance is primarily based on the company’s ability to keep controlled unclassified information confidential. Since a Public Key Infrastructure is crucial for issuing keys and certificates that are up-to-date, trusted, and compliant, defense contractors must utilize PKIs within their defense chain to ensure compliance.
These are some of the most important frequently asked questions and their answers relating to version 2.0 of the CMMC. These measures ensure proper cybersecurity measures are taken to protect controlled, unclassified information from the federal government and DoD.
READ MORE: Here are the Top 12 Tips for Better Communication with Your Partner